[TIL] Spring Advanced - JWT Authentication Flow
This is a TIL that summarizes the concept of JWT, reasons for use, and authentication flow from a Spring learning perspective.
한국어 원문은 여기에서 볼 수 있습니다.
[TIL] Spring Advanced - JWT Authentication Flow
What to do today
What I studied
###JWT
- JWT (Json Web Token)
- Claim-based Web Token that stores user properties using JSON format
- Typically stores JWT using cookie storage
Why use JWT
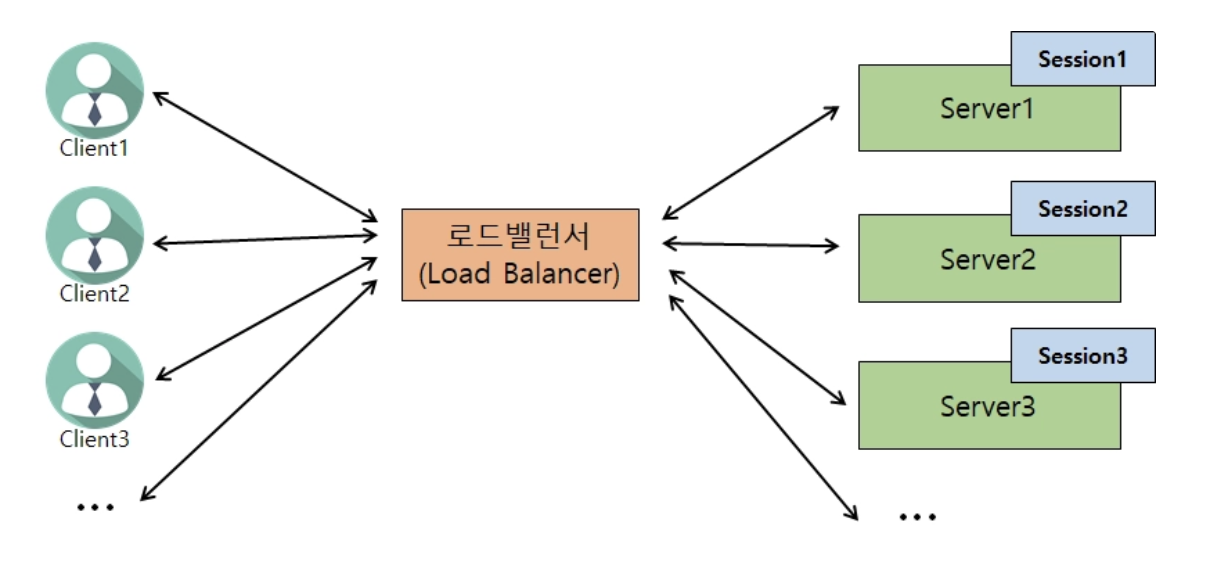
- When there is only one server
- Session1 owns all clients’ login information.
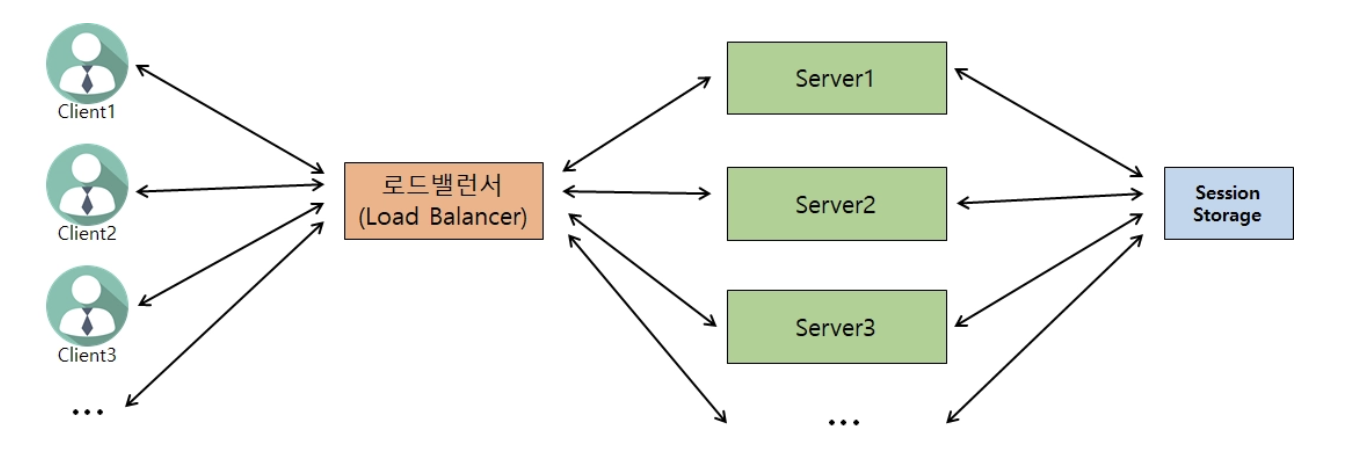
- When there are two or more servers
- Use JWT
- Instead of storing login information on the server, log-in information is encrypted and stored as JWT on the client -> Authentication/authorization through JWT
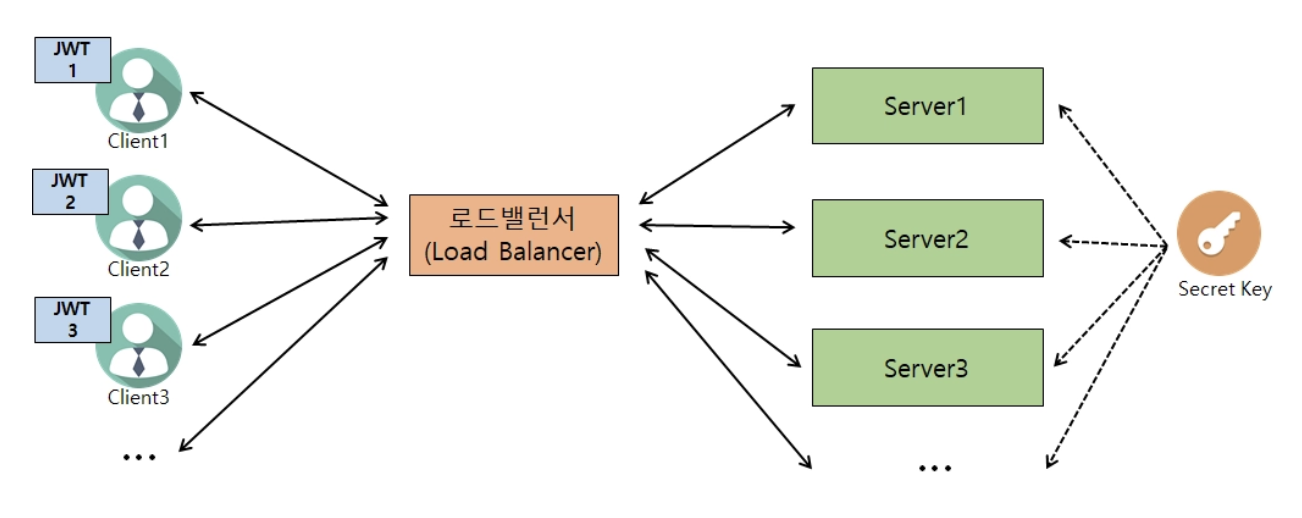
- All servers have the same Secret Key
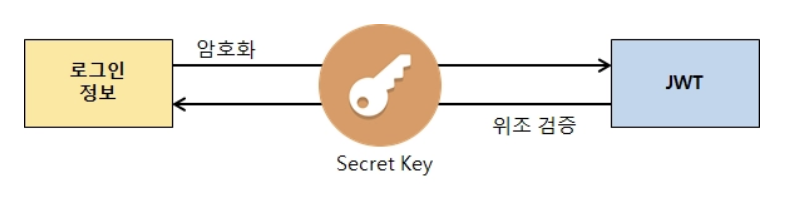
- Encryption/forgery verification through Secret Key (when decrypting)
- Advantages:
- Reduce server load when there are many concurrent users
- When the client and server use different domains ex) Use JWT Token when logging in to Kakao OAuth2
- Disadvantages:
- Increased implementation complexity
- As the content contained in the JWT increases, network costs increase (client -> server)
- There is no way to expire some of the already created JWTs
- JWT can be manipulated when secret key is leaked
- JWT usage flow
- Instead of storing login information on the server, log-in information is encrypted and stored as JWT on the client -> Authentication/authorization through JWT
- When the client successfully logs in with username and password a. ‘Login information’ on the server -> JWT encryption (using Secret Key) b. Create a cookie directly on the server and send it to the client response with JWT
- The JWT delivery method is determined by the developer.
1
2
3
4
5
6
7
8
9
10
c. JWT automatically stored in browser cookie storage 2. Authentication method through JWT from client
a. Every time an API request is made on the server, the JWT included in the cookie is found and used.
- Since there may be multiple pieces of information contained in a cookie, the JWT is retrieved by checking if the name of one of them is the same as the name of the cookie containing the JWT.
b. Server
- Verify whether the JWT delivered by the client is forged (using Secret Key)
- Verify that the JWT expiration date has not expired
- When verification is successful,
- Get user information from JWT -> and check